Roles & Permissions#
Roles#
This allows to set up Roles for the Konfuzio Server instance. Every Role contains Permissions. There are two ways to define Permissions. Project based Persmissions and global Permissions.
Project-based Permissions: Superusers, as defined by the Django documentation, can assign Permissions to Roles. Technically, those are called Role Permissions. Project-based Permissions define what a User is allowed to do as a member of a project. These Roles are set when inviting Members to Projects.
Global defined Permissions: Superusers, as defined by the Django documentation, can assign Permissions to Users via (https://docs.djangoproject.com/en/4.1/topics/auth/default/#groups) or directly to a User (without a Project context) as
Direct Permissions. Global permissions define which permissions one user has accross all projects.
Name [en]:#
The name of the Role.
Name [de]:#
The German name of the Role.
Role Permissions:#
All Permissions that belong to the Role.
Note:#
Roles are used to invite Users as Members to existing Projects. Therefore, the Permission “add_project” cannot be assigned to Roles. To decide if a User can create a new Project
Direct Permissionsare used.A User can be invited using a Role which does not include the “view_project” Permission. In this case the invited User can still see the Project name. However he cannot access any Project properties.
List endpoints (e.g. Projects, Categories, Documents, Labels, Label-Sets) show information across Projects. Therefore the direct Permissions are used to check if a user can access these information. An empty set is returned if the User does not have any Role Permissions.
Available Permissions#
Special Permissions:#
These type of Permissions cover view, change, add and delete rights related to certain user. In detail, these permissions refer to Konfuzio Server modules created by user, assigned to user, belonging to user or invited user.
General Permissions:#
Apart from the special permissions, for every Konfuzio Server Module view, change, add and delete are present as general Permissions.
Module Permissions:#
The Konfuzio Server modules mentioned in General & Special Permissions are defined as follows:
Annotations and Annotation Sets#
The access to Annotation / Annotations Sets can be limited to only these Annotation / Annotations Sets which are in Documents a User has access to (this is also considered by the ‘created_by’ and ‘assigned_to’ Permission).
can view annotation
can add annotation
can change annotation
can delete annotation
can view annotation belonging to user
can change annotation belonging to user
can delete annotation belonging to user
can view annotation set
can add annotation set
can change annotation set
can delete annotation set
can view annotation set belonging to user
can change annotation set belonging to user
can delete annotation set belonging to user
AI run#
can view AI model run
can add AI model run
can change AI model run
can delete AI model run
Categorization AI and Extraction AI#
The access to AIs can be restricted based on the User who started the AI training.
can view categorization AI
can add categorization AI
can change categorization AI
can delete categorization AI
can view categorization AI created by user
can change categorization AI created by user
can delete categorization AI created_by user
can view extraction AI
can add extraction AI
can change extraction AI
can delete extraction AI
can view extraction AI created by user
can change extraction AI created by user
can delete extraction AI created_by user
Category#
can view category
can add category
can change category
can delete category
Category Annotation#
can view category annotation
can add category annotation
can change category annotation
can delete category annotation
Deleted Annotation#
can view deleted annotation
can add deleted annotation
can change deleted annotation
can delete deleted annotation
Document#
The access to Documents can be restricted based on the creator and the assignee of a Document.
can view document
can add document
can change document
can delete document
can view document created by user
can change document created by user
can delete document created by user
can view document assigned to user
can change document assigned to user
can delete document assigned to user
change_document_dataset_status
Label#
can view label
can add label
can change label
can delete label
Labeling Tool Document#
can view labeling tool document
can add labeling tool document
can change labeling tool document
can delete labeling tool document
Labeling Tool Section#
can view labeling tool section
can add labeling tool section
can change labeling tool section
can delete labeling tool section
Members#
The access can be limited based on the invited User and the inviting User.
can view project invitation
can add project invitation
can change project invitation
can delete project invitation
can view member as invited user
can change member as invited user
can delete member as invited user
can view member as inviting user
can change member as inviting user
can delete member as inviting user
Missing Annotation#
can view missing annotation
can add missing annotation
can change missing annotation
can delete missing annotation
can view missing annotation belonging to user
can add missing annotation belonging to user
can change missing annotation belonging to user
can delete missing annotation belonging to user
Marketplace Listing#
can add listing
can view listing
can delete listing
Marketplace Access Request#
can add access request
can view access request
can delete access request
Page#
can view page
can add page
can change page
can delete page
Snapshot#
can view snapshot
can add snapshot
can change snapshot
can delete snapshot
Snapshot Restore#
can view snapshot restore
can add snapshot restore
can change snapshot restore
can delete snapshot restore
Project#
can view project
can add project
can change project
can delete project
Project Member#
can view project member
can add project member
can change project member
can delete project member
Rights Support#
access flower monitoring
access queue monitoring
access usage statistics
Role#
can view role
can add role
can change role
can delete role
Role Permission#
can view role permission
can add role permission
can change role permission
can delete role permission
Task Log#
can view task log
can add task log
can change task log
can delete task log
Text Document#
can view text document
can add text document
can change text document
can delete text document
Hint: In order to to use the SmartView the following Permisisons are needed:
can view project
can view label
can view label set
can view document or view document created by user or view document assigned to user
AI Upload Permissions#
These permissions control who can upload AI models via API:
can upload extraction AI - Allows uploading extraction AI models via API
can upload category AI - Allows uploading categorization AI models via API
can upload splitting AI - Allows uploading splitting AI models via API
How to get to the Roles#
The Superuser can create custom Roles. If you have Superuser rights, you will see under AUTHENTICATION AND AUTHORIZATION in the sidebar, the link to the Roles.
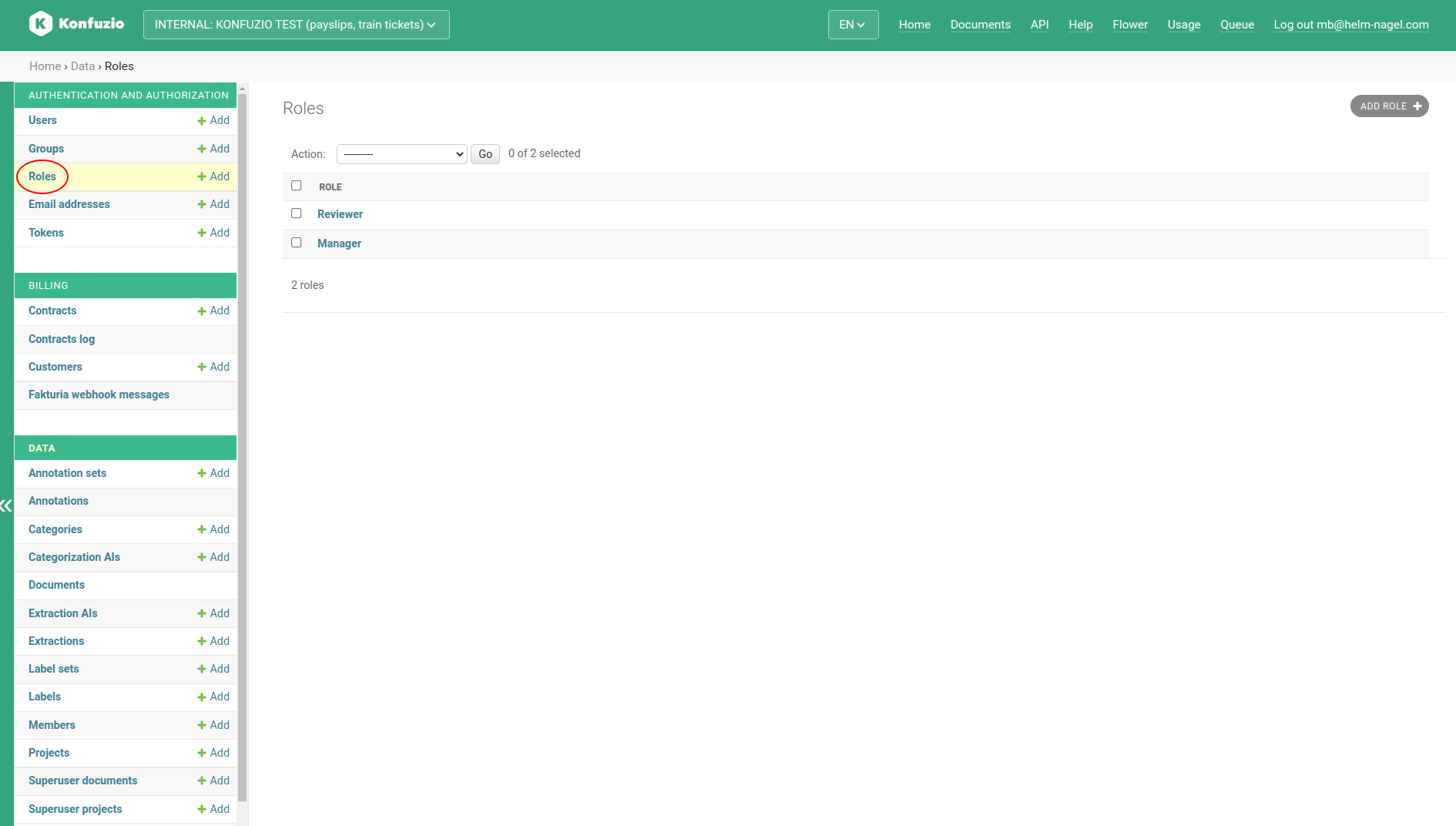
As soon as you have pressed the link of the Role, you will see the available Roles as shown in the graphic above.
How to create custom Roles#
To create a custom Role you have to click on the “ADD ROLE” button. After that, a Role name should be set and the creation is completed by clicking on “Save”.
How to assign Permissions to Roles#
Next, the Superuser can also assign the Permissions described above to the customly created or already existing Roles.
If you now click on these Role entries, a view opens in which you can see all the Permissions assigned to the Role:
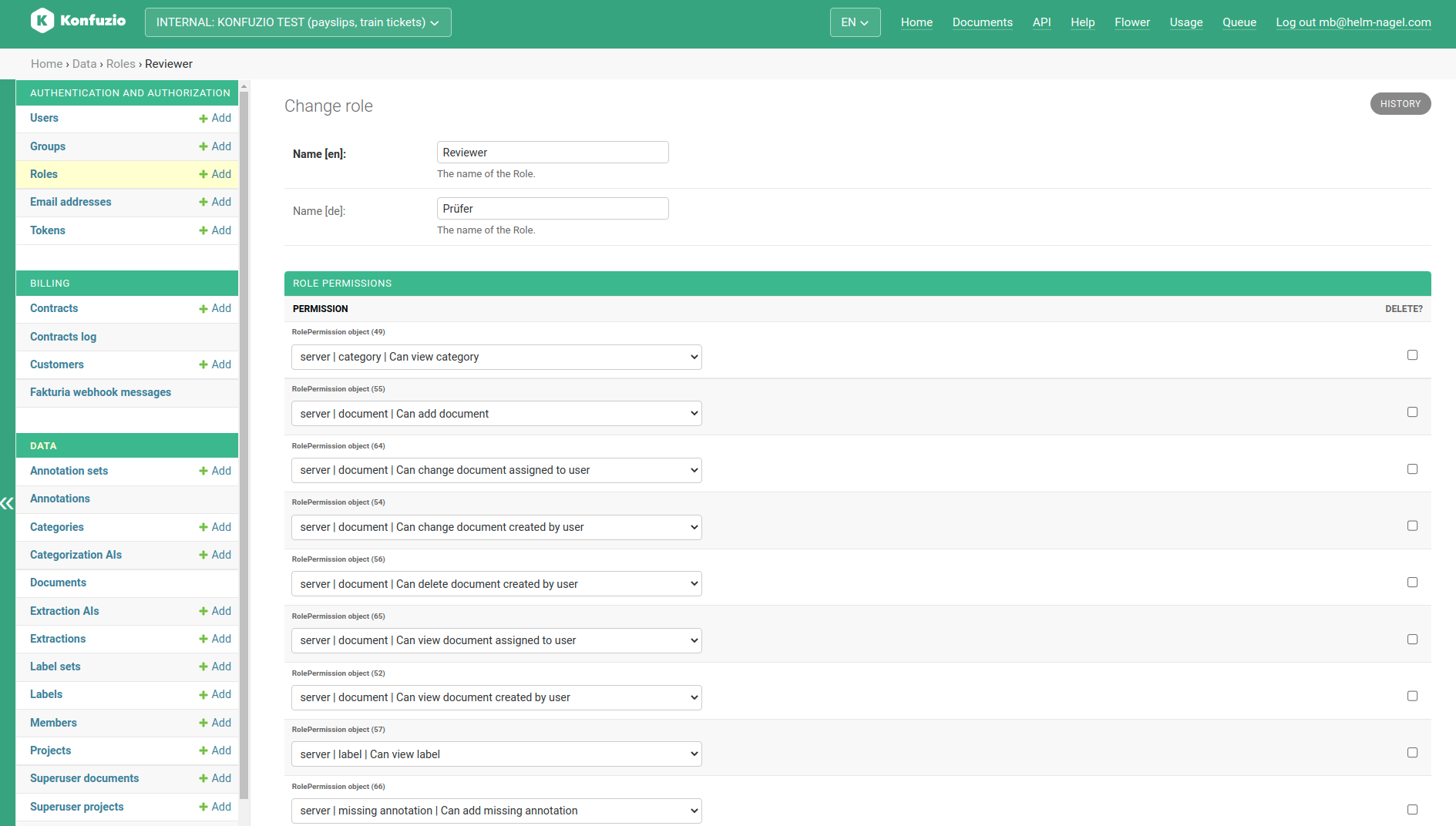
If you want to remove a Permission, click on the checkbox of the relevant Permission, scroll to the bottom of the list and then press “Delete”.
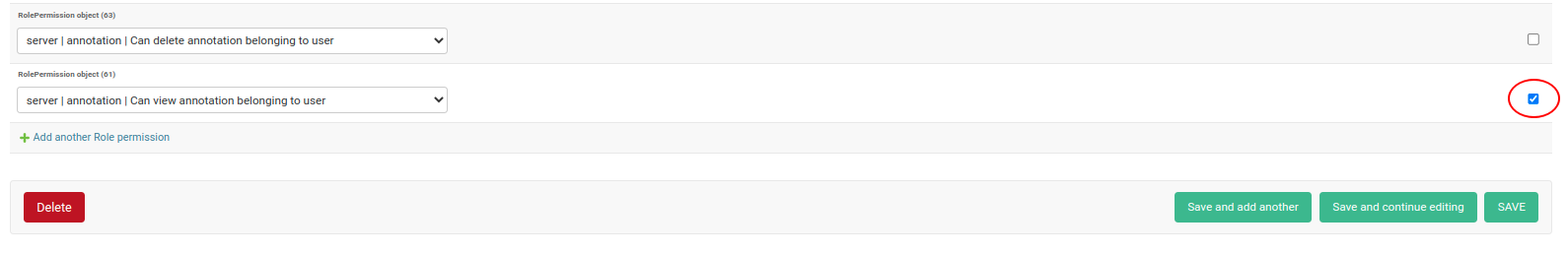
In addition to removing a Permission, you can also add more of the Permissions shown above, provided these are not already assigned to the Role. This is done via the “Add another Role permission” link at the end of the Permissions list, as shown in the graphic below:
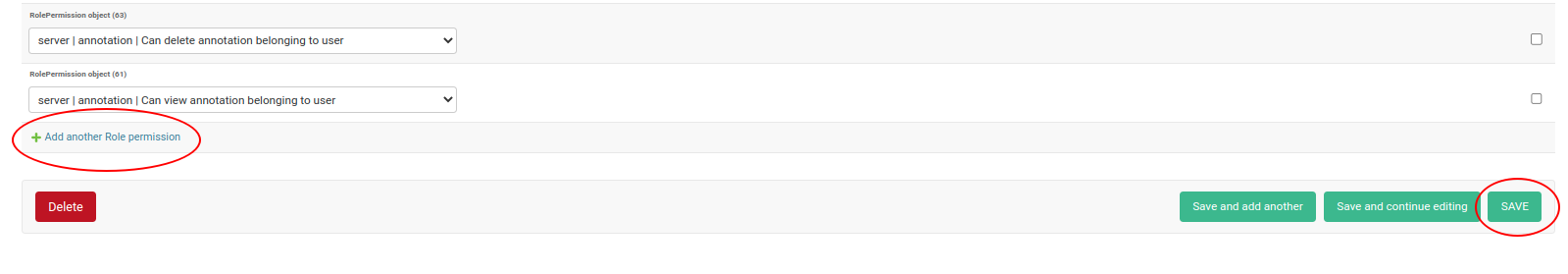
Finally, you only have to confirm the addition of the Permission with the “Save” button.
How Permissions are validated#
The given flowchart illustrates the permission structure within the Konfuzio Server. This flowchart is particularly useful for understanding how Permissions are managed when performing different operations (Create, Read, Update or Delete - CRUD) on various modules within the application (for instance, Document, Label, and so forth).
Below is a step-by-step description of the flowchart:
Create, Read, Update, or Delete (CRUD) operations: The process starts with the user performing one of the CRUD operations in the application.
Module Selection: The operation can be performed on different modules within the application such as Document, Label, and so forth.
Request: Once the user initiates a CRUD operation on a particular module, a request is created.
Global, Plan, and Role Permissions: This request is then verified across three different levels - Global Permissions, Plan Permissions, and Role Permissions.
Global Permissions: These Permissions apply to all users regardless of their specific roles or plan subscriptions. They determine what actions all users can take within the application.
Plan Permissions: These Permissions are dependent on the specific subscription plan a user has. They might vary according to the features and resources allocated to a particular plan. The available Plans for htpps://app.konfuzio.com are listed on https://konfuzio.com/price.
Role Permissions: These are related to the specific Role a user has within the application, for instance, Manager, Reviewer, Reader, etc. Different Roles have different sets of permissible actions.
Verify using ‘AND’: After the permission checks on all three levels (Global, Plan, Role), an ‘AND’ verification takes place. This implies that the request needs to pass all three checks to be allowed.
Allow or Deny: If the request passes all three Permission checks, it is allowed, and the operation is executed. If the request does not pass any one of the checks, it is denied, and the operation is not executed.
By understanding and following this flowchart, users and developers can better manage and troubleshoot permission-related issues within the Konfuzio application.